Leverage Cloud Services for Boosted Data Protection
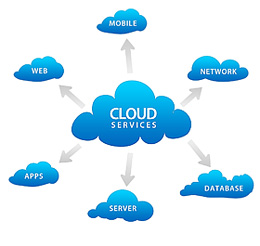
Leveraging cloud solutions provides a compelling service for organizations seeking to strengthen their information safety and security steps. The inquiry occurs: exactly how can the utilization of cloud solutions change information safety and security practices and supply a durable shield against prospective vulnerabilities?
Significance of Cloud Protection
Making certain durable cloud protection actions is vital in protecting delicate data in today's electronic landscape. As companies increasingly count on cloud services to save and process their data, the demand for strong safety protocols can not be overstated. A breach in cloud safety and security can have serious repercussions, ranging from monetary losses to reputational damage.
One of the main reasons cloud protection is essential is the shared obligation design utilized by many cloud company. While the supplier is in charge of safeguarding the infrastructure, customers are liable for protecting their data within the cloud. This department of duties underscores the relevance of carrying out durable safety procedures at the user degree.
Moreover, with the proliferation of cyber threats targeting cloud environments, such as ransomware and information breaches, organizations have to remain alert and proactive in mitigating dangers. This involves frequently updating safety methods, keeping track of for suspicious activities, and educating employees on ideal techniques for cloud safety. By prioritizing cloud safety, organizations can better shield their sensitive information and promote the count on of their stakeholders and consumers.
Information Security in the Cloud
File encryption in the cloud normally includes the use of cryptographic formulas to clamber information right into unreadable styles. In addition, several cloud service providers use security mechanisms to safeguard information at rest and in transit, enhancing overall data protection.
Secure Data Backup Solutions
Data backup services play a vital duty in guaranteeing the resilience and security of data in the occasion of unforeseen events or information loss. Secure information backup remedies are vital parts of a robust information safety technique. By on a regular basis backing up information to secure cloud web servers, companies can mitigate the threats connected with data loss due to cyber-attacks, equipment failures, or human mistake.
Carrying out safe and secure data backup solutions includes selecting dependable cloud service carriers that supply security, redundancy, and data integrity steps. In addition, data integrity checks make certain that the backed-up information remains tamper-proof and unchanged.
Organizations must develop automated back-up routines to ensure that information is consistently and efficiently supported without hand-operated treatment. When needed, regular screening of information remediation procedures is also crucial to assure the efficiency of the backup solutions in recovering information. By purchasing protected information backup remedies, businesses can boost their data safety and security posture and reduce the effect of prospective information violations or disturbances.
Role of Gain Access To Controls
Carrying out stringent accessibility controls is vital for maintaining the security and integrity of sensitive details within business systems. Accessibility controls work as an important layer of protection against unauthorized accessibility, making certain that only licensed people can see or adjust sensitive data. By defining who can gain access to particular resources, companies can restrict the risk of data violations and unapproved disclosures.

On a regular basis updating and assessing gain access to controls is necessary to adapt to organizational changes and advancing security dangers. Constant surveillance and bookkeeping of accessibility logs can assist spot any kind of questionable activities and unauthorized gain access to attempts without delay. Overall, robust accessibility controls are basic in safeguarding delicate info and mitigating protection threats within business systems.
Conformity and Rules
On a regular basis guaranteeing conformity with relevant policies and requirements is necessary for companies to maintain data security and privacy steps. In the realm of cloud services, where data is commonly kept and processed on the surface, adherence to industry-specific policies such as GDPR, HIPAA, or PCI DSS is crucial. linkdaddy cloud services press release.
Numerous suppliers use file encryption capacities, access controls, and audit routes to help organizations satisfy data safety and security requirements. By leveraging certified cloud services, organizations can improve their information safety position while satisfying regulative obligations.
Conclusion
In final thought, leveraging cloud solutions for check these guys out improved data protection is important for companies to protect sensitive information from unapproved gain access to and potential breaches. By carrying out durable cloud protection procedures, consisting of information encryption, protected back-up remedies, accessibility controls, and conformity with laws, businesses can gain from innovative safety and security procedures and know-how provided by cloud service carriers. This helps mitigate risks successfully and makes certain the privacy, integrity, and schedule of information.

Information back-up solutions play a crucial function in making sure the resilience and safety of information in look at this site the event of unanticipated cases or information loss. By regularly backing up data to secure cloud web servers, organizations can reduce the risks connected with information loss due to cyber-attacks, hardware failings, or human mistake.
Implementing safe information backup services entails selecting trusted cloud service companies that use encryption, redundancy, and information honesty procedures. By spending in protected data backup solutions, companies can enhance their information safety and security stance and decrease the influence of possible data breaches or interruptions.